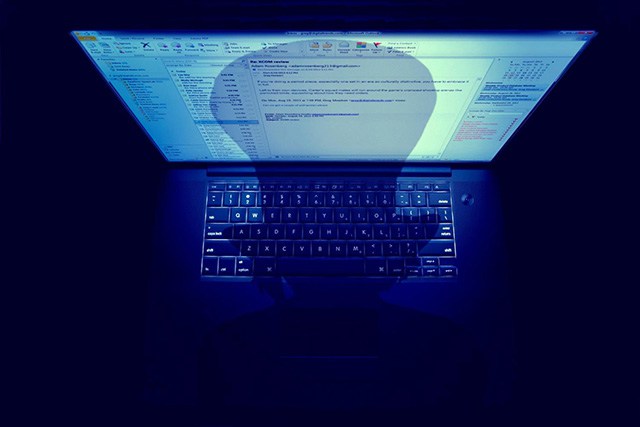
As much as you maybe want to believe your email is safe, it’s not… Prying eyes are watching you… Anyone who walks by your computer as you’re checking your email is privy to its contents; moreover, you could accidentally forget to log out of a public computer, malware could be recording screenshots and keystrokes, and (if unencrypted) your emails could be intercepted by unauthorized parties.
Data loss is a common issue, especially in regards to email. Accidental deletion is an example of email data loss, but all is not always lost in these situations. Email data recovery professionals can perform diagnostics and services in order to recover the lost data. And superior security software can ensure that your emails are encrypted and protected from malware attempts.
How to Keep Your Email Safe
Despite the fact that what’s lost can be recovered, it’s important to be proactive about email data protection. Take note of the Hillary Clinton email controversy? Presidential candidate Clinton used her family’s private email server to send official communications, including more than 2,000 emails which (once discovered) had to be retroactively marked as classified information.
Clinton’s use of her private servers has been widely debated because some members of congress believe that her actions violated State Department protocols, as well as some federal record-keeping laws. Although it’s debatable whether or not she was in compliance (she insists she was in compliance with federal laws), what’s not debatable is the security risks email poses.
Clinton was criticized for using her BlackBerry while appointed as Secretary of State. An unsecured BlackBerry poses a threat to security, and it’s just one example of how not secure email can be and how Clinton herself is fairly computer illiterate. She could have avoided the issue by not using personal email accounts for official business and ensuring that she was only corresponding about matters of national security from a federally sanctioned and secured computer.
You can avoid the issue of data hacking by avoiding transmitting sensitive emails on unsecured servers and unprotected mobile devices.

You can do everything on your end to protect your email, but if your recipient isn’t following a security protocol, you’re still at risk.
No matter what, it’s essential to encrypt your email. Especially in situations where your email correspondences include sensitive information, an encryption is vital to ensuring your emails aren’t intercepted by unauthorized third parties. As your email travels from the email server to its intended destination, if unencrypted it can be stolen by hackers. Only sign up for email with SSL-encrypted websites, which can be recognized by their link which begins with “https” instead of the unencrypted “http”.
Email Safety after Sending
You can do everything on your end to protect your email, but if your recipient isn’t following a security protocol, you’re still at risk. If your email account is on a private server, then you can manage your rights. Ask your IT team to include security features, such as a Do Not Forward option. This option ensures the email cannot be forwarded to others, nor can it be printed or copied from. You could also include something in the address bar that warns the user to read the email privately, such as “This email contains sensitive information,” or another type of warning that stops the recipient from reading it around prying eyes.
Also, and this is a big one, never ever transmit private information using a social media account. Facebook and other social media networks collect data on you, and they use it for their purposes… You don’t need that level of data breach in your life, and especially shouldn’t open your business up to it.
The rule of thumb here is to always assume the worst: nothing you email is truly private. Take proactive steps to ensure as much privacy as possible, but avoid transmitting anything that could damage your business or reputation. Change your password often, encrypt your data, and avoid opening your emails around lurkers and you should sufficiently minimize your security risk.
Other self-sufficiency and preparedness solutions recommended for you:
Healthy Soil + Healthy Plants = Healthy You
The vital self-sufficiency lessons our great grand-fathers left us
Knowledge to survive any medical crisis situation
Liberal’s hidden agenda: more than just your guns
Build yourself the only unlimited water source you’ll ever need
4 Important Forgotten Skills used by our Ancestors that can help you in any crisis